Single sign-on (SSO) is basically a technique to authenticate users and user sessions. This authentication service allows users to use the same credentials comprising the name and password for accessing several applications. SSO can benefit enterprises and individuals to reduce the negative impact on productivity created by different usernames and passwords for a variety of applications.
For the web SSO service to work effectively, an agent module is used for the particular application server that takes out the respective authentication credentials for the individual user. The service also helps the individual users to be authenticated by the repository of user credentials like the lightweight directory access protocol (LDAP) directory. This helps users get authenticated across applications while preventing future password prompts from appearing repeatedly.
Does SSO Reduce IT Costs? If Yes, How?
It has been seen that SSO has a positive impact on cost factors. The SSO service reduces the IT costs by simply allowing to prevent password reset instances. Any organization requiring different username and password separately for different employee and apps, it experiences an increase in the password reset instances which results in enhanced IT costs.
Thanks to SSO, users whether in an enterprise setting or outside only needs to remember just single credential for multiple apps and this obviously results in the reduced password reset requests. For an organization, this helps in reducing the involvement of the IT department resulting in cost advantages.
SSO Boosts Productivity and Usability
Thanks to the increasing use of cloud platforms, these days employees use a lot of apps than ever before and this requires using separate usernames and passwords for different apps resulting in increased task burden on the employees and reduced productivity in workplaces. A single sign-on not just lowers the cognitive burden, but also helps in boosting productivity to a great extent. By simply saving time for multiple logins, SSO simplifies employee engagement.
SSO for Enhanced Security and Compliance
One of the crucial advantages of SSO is the security enhancement that any mobile app development company is aware of. We all know that usernames and passwords are targeted by cybercriminals to get unauthorized access to the user data. Now, each time the user uses login credentials to log in to a new app, the user data becomes vulnerable to hacking and unauthorized access. SSO by simply allowing users to use a single set of credentials reduces this vulnerability and the instances of such cyberattacks to a great extent.
Simply, the reduction of all the different credentials for different apps to just one single set of credentials reduces the security vulnerability and security risks to a great extent. When employees in an enterprise setting need to use different credentials for different apps, it only enhances the security risks for enterprises as well. It has been seen that many employees simply to avoid complexity just uses the same easy to remember the password for multiple apps which further makes security setting vulnerable to cyber attacks.
Meeting Regulatory Compliance
SSO service also helps enterprises to meet regulatory compliance. Regulations like Sarbanes-Oxley need an enterprise to document all the IT controls for proving that the company is having appropriate methods in place for data protection. SSO is a great method to meet such regulatory requirements that rule data access and data protection measures.
SSO is also helpful in meeting various regulations such as HIPAA that suggests specific measures for user authentication and for access to electronic data. Regulations such as HIPAA also need automatic log off from the user sessions that SSO service provides.
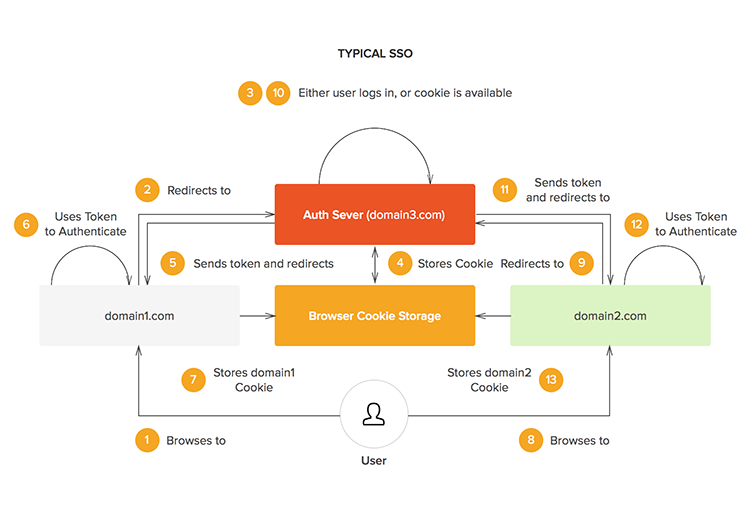
How SSO Service Works?
Single sign-on or SSO works basically as a federal identity management instrument. It is important to know the technical attributes and how it works to manage authentication measures in a comprehensive manner.
OAuth is a framework that works as an intermediary solution to provide an access token to the end-user for sharing the specific account data with third-party apps. As and when the user tries to log in an app, the service provider will request the identity provider for the respective credential data. Upon getting the data the service provider will verify the information and Allie users to log in.
Let Us Briefly Explain The Steps for implementing SSO.
- To begin with, evaluate the goal of SSO service and accordingly opt for the options that are most beneficial for your user context.
- Secondly, you need to know users and requirements, the typical capabilities and analyze where the service needs to breach the gaps. Here you also need to evaluate the SSO requirements of the company.
- Now, you need to create an architecture for providing support to SSO. You need to take a call on whether you need on-premise SSO software or a cloud-based service or a hybrid approach.
- Now, you need to assess the specific access control needs for SSO. Since, proper authentication is crucial for achieving the objective of the service, a flexible trust-based approach for user authentication is more effective.
- At this step, you need to assess all other associated technical requirements apart from the general architecture. This includes access to APIs, Microsoft Office 365 and Amazon Web Services (AWS).
- Now, you need to work upon refining the architecture with iteration. Since giving access to all apps for all employees is not necessary, you need to figure out who needs and accordingly implement the service around the world.
Conclusion
SSO or single sign-on technology is here to stay. Single sign-on or SSO simply seems to be an irreplaceable technology for the apps across enterprises.